Increasing the Netherlands’ DDoS resilience together
First lessons learned from setting up a national anti-DDoS initiative, part I of III
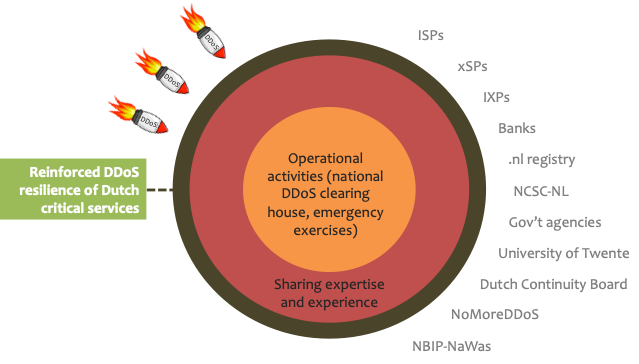
The Dutch Anti-DDoS Coalition is a national consortium of seventeen organisations from various sectors (e.g. ISPs, banks, government agencies and law enforcement) committed to fighting DDoS attacks together. In this series of three blogs, we’ll first discuss the rationale behind our initiative, then describe a technical facility called the DDoS clearing house that enables coalition members to automatically measure and share the properties of DDoS attacks (e.g. attack duration and source IP addresses), before finally reviewing our key challenges, the lessons learned and the way forward. Our lessons learned are an important input for a “cookbook” to set up anti-DDoS coalitions elsewhere in Europe.
Note: we’re using two types of reference in this blog series: hyperlinks refer to more high-level background information, while numbers between straight brackets ([]) link to in-depth technical material such as academic papers.
DDoS attack landscape
A Distributed Denial-of-Service (DDoS) attack overwhelms a network with traffic, thus denying servers connected to the network the ability to service legitimate requests from their clients. The attacker typically accomplishes this by simultaneously transmitting traffic from a large number of machines distributed across the internet to the target, for example by infecting those machines with malware that carries out the attack. Another type of DDoS attack is when the attacking machines exhausts a server’s resources (rather than swamping the network) [DDOS13]. For example, the attacker could repeatedly start a logon session with the server, thus forcing it to make many demanding computations such as database lookups to get usernames and user credential checks. As a result, the server uses up its resources (e.g. TCP connections, memory and CPU cycles), so it is unable to serve legitimate user requests.
The most recent large-scale DDoS attacks in the Netherlands took place in January of 2018 and caused disruption to financial, government and other services. The alleged attacker suggested that he had bought the attack capacity online “as a service” for just forty euros.
Cooperative DDoS mitigation to the rescue
While DDoS attacks have been around for a long time and are routinely handled by specialised services (e.g. NBIP-Nawas or commercial equivalents such as Akamai and Cloudflare), we expect the risk they pose to society to increase. For example, on the Internet of Things (IoT), a DDoS attack might take out the remote services that the smart traffic lights in a city depend on to work safely and correctly. At the same time, the IoT itself also poses a risk [SAC105] because it enables DDoS attacks from large numbers of insecure IoT devices that are typically difficult to fix in bulk, for instance because they operate autonomously or because they lack a standardised firmware update mechanism [FW19].
One potentially effective way to counter such attacks is for service providers to fight DDoS attacks on a collaborative basis. The concept of collaborative defence has been around for a long time [DDOS13] [BloSS19] but has not yet been widely adopted. Instead, service providers currently mitigate DDoS attacks single-handedly, focusing on protecting their own infrastructures. Some do nevertheless participate in group protection services such as NBIP-Nawas to share equipment and expertise, and to spread the cost.
Dutch Anti-DDoS Coalition
In the Netherlands, we decided after the January 2018 DDoS attacks that things needed to change. Specifically, we decided to put the concept of cooperative DDoS mitigation into operation at the national level. To that end, we set up the Dutch Anti-DDoS Coalition, a national voluntary consortium of seventeen organisations from a wide variety of sectors. The coalition members include ISPs, banks, internet exchanges and government agencies.
While the backgrounds of the coalition members differ greatly, they share a common goal:
To realise our goal, the coalition has adopted a two-layer membership model (Figure 1). The core consists of members who cooperate through operational activities: they measure and share DDoS attack properties and they jointly carry out large-scale DDoS drills (more on both in Part II and Part III). The other members focus on sharing expertise on responding to DDoS attacks.
Members organise themselves into working groups, such as a technical working group to develop and operate the technical facilities for sharing DDoS measurements, a legal working group to develop and evolve information sharing agreements, and a ground rules working group to formalise our coalition procedures. Our organisational structure is informal at the moment, but we may turn it into a (dedicated) legal entity in the future when more members join.
Cookbook for other European Member States
Our lessons learned (e.g. technical, legal, and organisational) will be an important input for a “cookbook” to set up anti-DDoS coalitions elsewhere in Europe. SIDN, SURF, and the UT will develop the cookbook together with partners like Telecom Italia as part of CONCORDIA, a research project with over 50 partners from industry and academia that focuses on data-centric cybersecurity and aims to set up a leading cybersecurity network of excellence for Europe.
Next week
In our next blog of this series, we’ll zoom in on the clearing house, the technical system that we’re building to measure the properties of DDoS attacks and share them among coalition members.
Acknowledgements
SIDN, SURF and the University of Twente were partly funded by the European Union’s Horizon 2020 Research and Innovation programme under Grant Agreement No 830927. Project website: https://www.concordia-h2020.eu/
References
[DDOS13] Saman Taghavi Zargar, James Joshi and David Tipper, “A Survey of Defense Mechanisms Against Distributed Denial of Service (DDoS) Flooding Attacks”, IEEE Communications Surveys & Tutorials, Vol. 15, Issue 4, 4th Quarter 2013
[FW19] B. Moran, H. Tschofenig, D. Brown and M. Meriac, “A Firmware Update Architecture for Internet of Things Devices”, draft-ietf-suit-architecture-05, April 2019
[SAC105] T. April, L. Chapin, kc claffy, C. Hesselman, M. Kaeo, J. Latour, D. McPherson, D. Piscitello, R. Rasmussen and M. Seiden, “The DNS and the Internet of Things: Opportunities, Risks, and Challenges”, SSAC report SAC105, June 2019, https://www.icann.org/en/system/files/files/sac-105-en.pdf
[BloSS19] Bruno Rodrigues and Burkhard Stiller, “Cooperative Signaling of DDoS Attacks in a Blockchain-based Network”, SIGCOMM Posters and Demos ’19: Proceedings of the ACM SIGCOMM 2019 Conference Posters and Demos August 2019, https://doi.org/10.1145/3342280.3342300
(By Cristian Hesselman (SIDN and University of Twente), Remco Poortinga-van Wijnen (SURF), Gerald Schaapman (NBIP) and Remco Ruiter (Dutch Payments Association))
